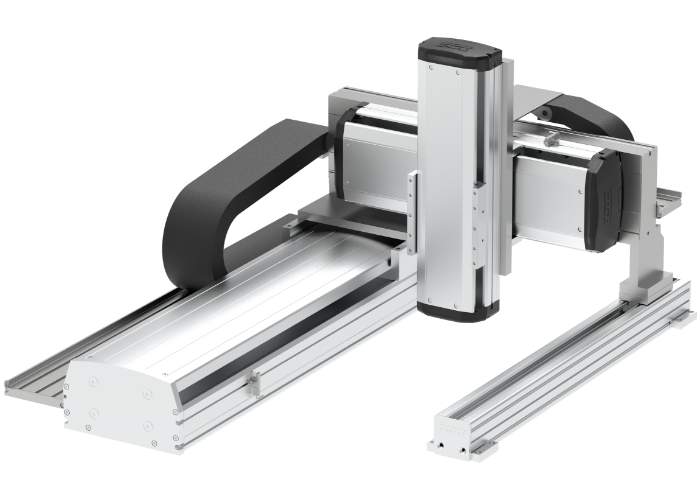
Danh mục sản phẩm toyorobot
How Math Keeps Your Data Safe with Fish Road
1. Introduction: The Intersection of Mathematics and Data Security
In our increasingly digital world, safeguarding personal and organizational data is paramount. Behind the scenes, complex mathematical models form the silent backbone of secure communication. The Fish Road model, introduced in the early foundations of secure routing, exemplifies how discrete geometry and graph theory translate into robust encryption strategies. At its core, Fish Road uses mathematical assumptions about network topology to define secure paths—each route representing a sequence of nodes connected through finite fields and modular arithmetic. These choices ensure that data traverses only authorized, verified nodes, minimizing exposure to interception. Explore the mathematical roots of Fish Road’s secure path model here.
2. Core Mathematical Tools: From Symmetric Keys to Post-Quantum Algorithms
The Fish Road framework relies on finite fields and modular arithmetic to encrypt and authenticate data at each node. These structures—central to modern cryptography—enable operations that are computationally easy to perform in one direction but infeasible to reverse without the correct key. Symmetric algorithms like AES use substitution-permutation networks grounded in these fields, while asymmetric systems such as RSA and elliptic curve cryptography depend on the hardness of integer factorization and discrete logarithms. As threats evolve, so do these tools: lattice-based cryptography, rooted in high-dimensional geometry, now promises encryption secure against quantum attacks, extending the legacy of Fish Road’s mathematical foresight.
Lattice problems, for instance, leverage the geometric complexity of high-dimensional vector spaces—mirroring Fish Road’s network integrity constraints—to build encryption schemes resistant to quantum algorithms. This mathematical evolution ensures that the principles of secure routing mature into next-generation privacy architectures.
3. Dynamic Threat Landscapes: Adapting Mathematical Models to Evolving Cyber Challenges
Modern cyber threats grow in sophistication, demanding adaptive mathematical defenses. Complexity theory formalizes the computational hardness assumptions underpinning today’s cryptographic protocols—ensuring that cracking encryption remains intractable even with exponential increases in processing power. Probabilistic algorithms, such as those used in zero-knowledge proofs, allow one party to verify knowledge of data without revealing it, a concept deeply tied to modular arithmetic and statistical randomness. These techniques fortify data integrity and user privacy in decentralized environments, where trust is derived not from central authorities but from validated mathematical proofs.
Zero-knowledge proofs, relying on elliptic curve discrete logarithms, exemplify how Fish Road’s topological rigor extends into interactive cryptographic protocols. By enabling secure authentication without data exposure, they embody the ongoing mathematical commitment to privacy in dynamic threat scenarios.
4. Bridging Past and Future: How Fish Road’s Legacy Informs Next-Generation Privacy Systems
Fish Road’s graph-based security was pioneering in its time, modeling secure data flow through physical or logical topologies. Today, this concept evolves into decentralized networks where nodes are not fixed but dynamically chosen, requiring advanced mathematical modeling to assess attack surfaces. Formal verification methods—using logic and proof theory—now rigorously validate these systems, ensuring that security properties hold under all conceivable conditions. By integrating mathematical rigor with real-world usability, modern privacy frameworks honor Fish Road’s vision while addressing challenges of scale, resilience, and user trust.
- Formal verification reduces implementation flaws by modeling system behavior mathematically.
- Decentralized identity systems use graph theory to manage trust without centralized control.
- Hybrid encryption schemes blend symmetric speed with asymmetric security, rooted in finite field operations.
“Mathematics transforms abstract topology into tangible security—guiding how data moves, verifies, and remains private across evolving digital landscapes.”
5. Practical Implications: Applying Encrypted Communication Principles in Real-World Settings
In secure messaging apps, IoT ecosystems, and financial transactions, Fish Road’s mathematical principles manifest through encrypted routing, device authentication, and transaction verification. For example, end-to-end encrypted messaging uses elliptic curve cryptography to ensure only intended recipients decrypt messages—leveraging modular exponentiation for secure key exchange. In IoT, lightweight cryptographic protocols rooted in finite fields enable secure communication on constrained devices without sacrificing performance. However, balancing mathematical complexity with usability remains a key challenge: overly intricate systems can deter adoption or create vulnerabilities through poor implementation.
| Real-World Application | Mathematical Foundation | Security Benefit |
|---|---|---|
| Secure Messaging | Elliptic Curve Cryptography (ECC) | Strong encryption with smaller key sizes for efficient, private communication |
| IoT Device Authentication | Finite Field Arithmetic | Lightweight, fast verification preventing spoofing and unauthorized access |
| Financial Transactions | Zero-Knowledge Proofs | Verifiable transactions without exposing sensitive data |
These applications demonstrate how Fish Road’s mathematical insight evolves into practical tools that empower digital trust across sectors, reinforcing data safety in real time.
Conclusion: The Mathematical Journey from Fish Road to Future Privacy
From discrete graphs to quantum-resistant algorithms, mathematics remains the silent guardian of digital security. Fish Road’s legacy endures not as a static model but as a foundation for adaptive, resilient systems. As cyber threats grow more sophisticated, the principles of discrete geometry, modular arithmetic, and complexity theory continue to guide innovations that protect data across physical and virtual domains. By grounding privacy in rigorous mathematical frameworks, we build communication networks that are not only secure, but trustworthy—ensuring that every message, transaction, and connection stays protected by design.
Return to the parent theme: How Math Keeps Your Data Safe with Fish Road